Livestream, Tuesday, 5:00 PM EST: Review of Appalling "CTI Files" Documents
In a joint exposé with Public, Michael Shellenberger, Alexandra Gutentag and I report on a damning new cache of whistleblower documents. Join a livestream as I walk through the most appalling material
This morning, Michael Shellenberger and Alexandra Gutentag published a piece on Public about a sizable new cache of documents, involving a group ostensibly dedicated to fighting Covid-19 misinformation called the CTI League (CTIL). You’ll find my byline on the story, as I came in after the fact to help review the enormous quantity of material provided by a whistleblower from the group. Tonight, I’ll be going through the documents at 5:00 ET, in another livestream. Click here tonight: this one should be very entertaining.
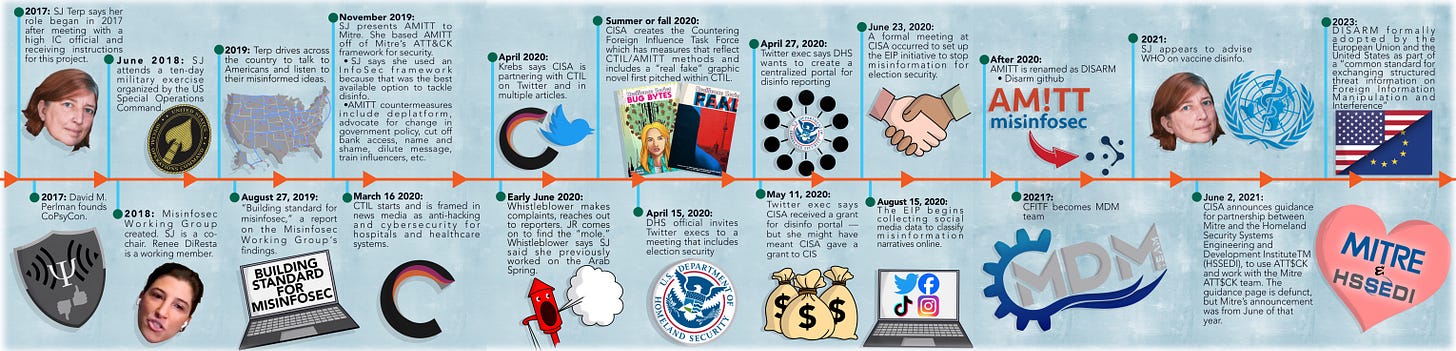
I was initially dismissive of the #CTIFiles as a news story, as were a few industry experts I consulted. The key figures behind the group — a British data scientist and former defense researcher named Sara-Jayne “SJ” Terp and a Navy/SOCOM “technologist” named Pablo Breuer — were not roundly considered by my sources to be heavy hitters in the anti-disinformation world. However, once we got into the documents, we all realized they had tremendous significance. It wasn’t just that CTIL’s virtual meetings and training sessions were routinely attended by DHS and FBI officials, or that Cybersecurity and Infrastructure Security Agency (CISA) head Chris Krebs announced that the DHS sub-unit was partnering with the group, or even that CTIL tactics were ultimately adopted at least in part by CISA.
No, the crucial element of the #CTILeague docs is that they show in great, gory detail a side of the anti-disinformation universe until now mostly hidden from the public. While the Twitter Files were important in confirming government involvement in defensive activities like censorship and deamplification, the #CTIFiles show how members were instructed in a wide range of offensive tactics, including everything from using burner phones to creating fake identities and sockpuppet accounts to infiltrate domestic political groups. CTIL trainings include instructions on “OpSec” with lines like “lock your shit down” and titles like “Persona: your spy disguise.”
The sheer size of this leak means it’s going to take a while to sort out everything and elevate the most explosive material, but at minimum, these files show that the FBI and DHS were enthusiastic partners with a group that openly embraced offensive tactics and spoke proudly of trying to build a “good guy analog” to the disinformation programs of states like Russia and China. One CTIL training begins with a quote from a 2007 Pentagon guide to “Electronic Warfare,” defining countermeasures as “the employment of devices and/or techniques, has [sic] as its objective the impairment of the operational effectiveness of enemy activity”:
This slide was shown to people whose job was reviewing domestic speech, tracking hashtags like #WeWontStayAtHome to #MinneapolisisBurning to the US Campaign for Palestinian Rights (@USCPR_). They used spy techniques at home, compiled and embraced a long list of “counter” techniques, and openly spoke about American citizens as “the enemy,” in the military sense of the word. And that’s just the beginning. The documents are full of other eyebrow-raising assertions, some of which will come out in this space (and in accompanying social media threads) in the next hours and days.
In the meantime, please check out the Public piece if possible, and stay tuned here at Racket, as there’s a lot more to come on this crazy story.





What does a huge, secretive, lavishly funded military-security apparatus do when it can't find a real, credible enemy to fight?
It turns on the people it is supposed to protect and declares them the enemy.
Thanks again. You fucking rule. Best $5 month ever.